Industrial Internet of Things (IIoT) Data Security:
The Unique Landscape of IIoT Security Risks, Challenges and Threats
Industrial Internet of Things (IIoT) Data Security:
Why IIoT Data Security Matters More Than Ever
by Dr. Serap OĞUZ TANATAR published September 9, 2025

Imagine critical production lines coming to a halt due to a cyberattack, resulting not only in millions of dollars in losses but also in weeks of disruption across the supply chain. In such scenarios, IIoT systems are vital not only for data security but also for maintaining operational continuity.
In the previous post of this blog series, we discussed the fundamental concepts of IIoT data security and examined how IIoT systems differ from traditional IT systems. We highlighted that real-time data flows, cyber-physical integration, and the continuity of critical processes in IIoT environments redefine the approach to data security. In this section, we take a step further by exploring the key challenges in ensuring security within IIoT environments, the unique risks to these systems, and the common attack vectors they face.
What are the challenges in ensuring IIoT security?
The challenges of securing IIoT environments stem from the nature of industrial operations, the devices involved, and the inherent risks of cyber-physical systems:
Complexity and Scale
The sheer number of interconnected devices, systems, and networks in IIoT environments results in an incredibly complex and challenging security landscape, significantly expanding the overall attack surface. This vast scale inherently makes comprehensive monitoring and management difficult. Moreover, with IIoT devices often geographically dispersed -like sensors spread across an oil field- reliable remote management systems are paramount for keeping security systems updated and ensuring proper device maintenance.
Legacy Systems Integration
A significant challenge arises from the widespread use of legacy systems in industrial facilities. Many machines operate with outdated hardware components and old software that contain known vulnerabilities (IOTSI, n.d.). These legacy systems often lack modern security features, making them inherently vulnerable to attacks when connected to contemporary networks. The pervasive integration of legacy systems that are often insecure by design and lack basic security functions directly results in a landscape riddled with unpatched vulnerabilities. This means that patching, a cornerstone of IT security, is often not viable, leading to a perpetual state of vulnerability that must be managed through external means.
Operational Constraints
Industrial environments impose unique operational constraints that complicate security efforts. Patching difficulties are prominent; stopping a device or halting systems for a patch may disrupt the entire production line. Moreover, patching IIoT systems often requires specialized technicians from vendors to carry out updates properly, making it a complex and time-consuming process. This frequently leads to devices operating for months or even years with unpatched vulnerabilities (Trend Micro, 2019).
Proprietary software and vendor dependencies further compound these issues. Industrial facilities often run on a range of proprietary software from multiple vendors. This software is frequently difficult to update and patch because vendors maintain control over them, leaving the IIoT particularly vulnerable if vendors are slow to release updates or if firmware updates are maliciously hijacked (Trend Micro, 2019).
Human Factors
Human error remains a substantial security risk in IIoT environments. User awareness about IIoT security issues, and even expertise in remediating IIoT security gaps, is notably low across all user communities (World Economic Forum, 2018). This lack of awareness, coupled with a significant skills gap in cybersecurity expertise, means that personnel may inadvertently introduce vulnerabilities or fail to follow secure protocols. Furthermore, "inside jobs" represent a considerable threat, with documented examples of terminated engineers remotely shutting down industrial operations (Thryft, 2018). The confluence of low user awareness, a skills gap, and the prevalence of default settings on IIoT devices creates a critical vulnerability that is often overlooked in favor of purely technical solutions (Nasstar, 2025).
This suggests that even with advanced security technologies, human factors can be the weakest link, necessitating robust training programs and strong policy enforcement as foundational security controls. When multiple sources point to human-related issues—low awareness, skills gap, and default passwords—it indicates that these are not merely technical vulnerabilities but failures in human and process management. If users do not understand the risks or fail to implement basic security hygiene, even the most sophisticated systems can be compromised, implying that security strategies must be holistic, addressing people and processes as much as technology.
Data Integrity and Privacy
Inadequate data encryption is a common oversight in the rush to deploy new technologies, leaving sensitive data vulnerable to interception and manipulation.
What are the common threats in IIoT environments?
The interconnected nature and unique vulnerabilities of IIoT systems make them attractive targets for cyberattacks. Therefore, having a clear understanding of common attack types and the methods used is critical for developing effective defense strategies.
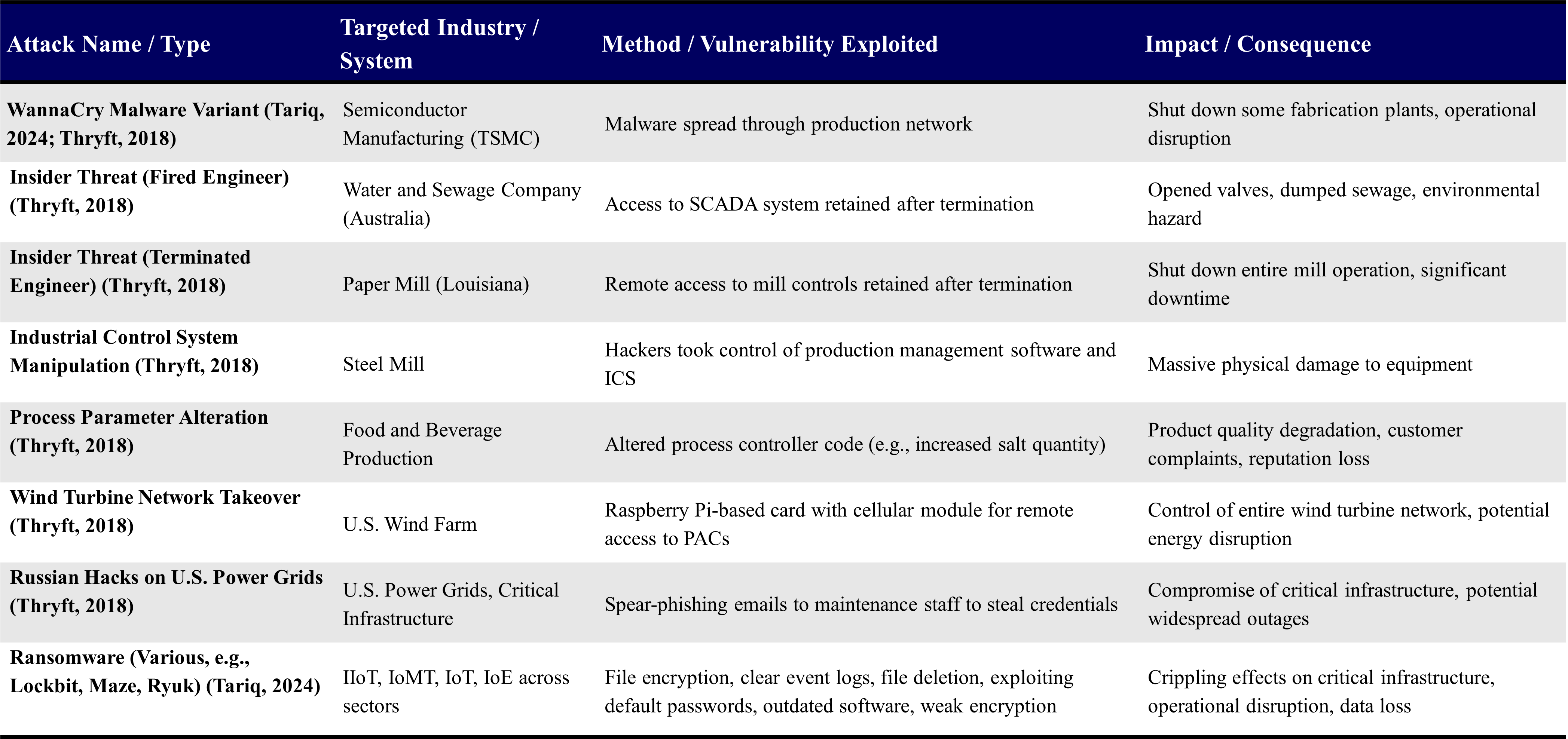
The table below provides concrete examples of IIoT cyberattacks, illustrating the diverse methods used by threat actors and the severe, real-world consequences they can inflict.
Malware and Ransomware
Ransomware attacks remain one of the most common methods used by malicious actors. The reason is their “dual payoff”: both encrypting and exfiltrating data while simultaneously causing operational disruption (Asimily, n.d.). Well-known ransomware families such as WannaCry, NotPetya, Ryuk, and Locky have exploited both known and zero-day vulnerabilities, creating devastating impacts on critical infrastructure (Tariq, 2024).
Different types of malware are widely employed to carry out various attack vectors. For example:
- InfoStealer: Collects session data such as usernames and passwords from compromised devices.
- Botnet: Enables attackers to establish remote control over devices.
These malicious programs also pave the way for further attacks, such as:
- Password Guessing Attacks: Common weak passwords are automatically tested to gain access.
- Impersonation Attacks: Stolen credentials are used to impersonate legitimate users.
The irregular modernization of industrial systems, combined with the insufficient security of many IIoT devices —for example, being shipped with default passwords, running outdated software, and employing weak encryption— has made these environments increasingly attractive to cyber attackers (Tariq, 2024).
As a result, attackers are strategically shifting toward OT and IIoT domains, which are less protected than traditional IT systems yet have a far greater impact. The potential consequences of physical disruptions make ransomware a highly effective tool of coercion in these areas. Attackers aim to achieve maximum impact with minimal effort; since industrial systems are poorly protected and breaches can cause severe physical or financial damage, these systems represent highly lucrative targets. The “two-for-one advantage” of ransomware —data encryption and operational shutdown— clearly demonstrates this reality.
Unauthorized Access
Users’ failure or negligence in changing default passwords constitutes a critical vulnerability, as it enables unauthorized access to system control mechanisms. Weak authentication systems and the absence of multi-factor authentication (MFA) provide attackers with easy entry points.
Many IIoT systems rely on Application Programming Interfaces (APIs) for communication between devices. If these APIs are not securely configured, they become easy targets for attacks such as:
- SQL Injection: May lead to the exfiltration of sensitive information from databases.
- Distributed Denial of Service (DDoS) Attacks: Overloads systems to the point of service unavailability (IIoT Security, n.d.).
Eavesdropping and Man-in-the-Middle Attacks
Attackers can capture previously transmitted legitimate messages over wireless networks and resend them after modification. Such attacks are known as “replay attacks.”
Additionally, attackers can intercept data transfers between devices by scanning networks. This type of attack is referred to as a “man-in-the-middle” attack. These attacks compromise both data integrity and confidentiality (Asimily, n.d.).
Poorly configured systems or flawed communication protocols can render both data and devices accessible to attackers.
Supply Chain Attacks
A growing concern is the increasing trend of attackers hijacking firmware updates to insert malware onto devices before they are deployed. Compromising devices or software at any point in the supply chain can impact the integrity of the entire system, creating a backdoor for future attacks.
Denial of Service (DoS) Attacks
Denial of Service attacks are designed to cripple a target host by overwhelming it with so much traffic that it cannot handle the volume. In IIoT, these attacks can disrupt critical industrial processes and potentially cause significant outages across multiple sectors.
In the next post of the series, we will discuss strategies and solutions that can be implemented to ensure data security in IIoT environments, as well as industry standards and governance approaches that reinforce security.
References
Asimily, (n.d.). 6 Common IIoT Cyberattacks Manufacturers.
Gargan, R. (2024). IIoT Security. Netmaker.
IOTSI. (n.d.). Guide tı IIoT Security Best Practices, Use Cases, and Mitigation Strategies. IoT Security Institute.
Nasstar. (2025). The Ultimate Guide to IIoT Security: Challenges & Solutions.
QuestDB. (n.d.). Industrial IoT (IIoT) Data.
Tariq, U. (2024). Combatting ransomware in ZephyrOS-activated industrial IoT environmetns. Heliyon. 2024 Apr 22;10(9):e29917.
Thryft, A. R. (2018). Real-life Industrial IoT Cyberattack Scenarios. EE Times.
TME Systems. (2025). Industrial IoT Security.
Trend Micro. (2019). The IIoT Attack Surface: Threats and Security Solutions.
World Economic Forum. (2018). The IIoT Safety and Security Protocol.
